| Subtotal | $0.00 |
| Subtotal | $0.00 |
In this guide we will show possible ways of enabling SSL/TLS encryption with a trusted SSL certificate for incoming and outgoing connections on a typical Postfix-Dovecot mail server.
We have used a PositiveSSL certificate for testing; however, any certificate offered at Namecheap is capable to secure the mail server of this type. Testing was performed on the following server stack:
If you do not have an issued SSL certificate for your mail server hostname so far, feel free to purchase one, generate a CSR code and activate it.
When the certificate is issued, it can be downloaded from the Namecheap user account or from the fulfillment email sent by the Certificate Authority to the certificate’s administrative contact email address.
Uploading and concatenating certificate files on the server
To check the content of the newly created file, run cat /etc/ssl/certs/certificate.crt or cat /etc/ssl/certs/certificate_and_key.crt. Make sure that the output does not contain excessive white spaces between or inside the PEM-encoded certificate and key blocks. If you spot the spaces, you can open the file in a text editor like “vi” or “nano” and remove them manually.
Editing Postfix and Dovecot configuration files to enable SSL/TLS on specific ports
Sending and receiving mail over the Internet relies on a complex system of endpoint and intermediary instances (mail server and client software) labeled as mail user agents (MUA), mail submission agents (MSA), mail transfer agents (MTA) and mail delivery agents (MDA) depending on the functions they perform. Normally, an email is passed over each type of the above mentioned parties, and different transport protocols are used on every step, namely submission protocol, Simple Mail Transfer Protocol (SMTP), Post Office Protocol (POP3) and Internet Message Access Protocol (IMAP).
The table below specifies the ports use for specific transport protocol execution.
| Protocol | Usage | Plain text/encrypted session | Encrypted session only |
|---|---|---|---|
| POP3 | Incoming mail | 110 | 995 |
| IMAP | Incoming mail | 143 | 993 |
| SMTP | Outgoing mail | 25 | 465 |
| Submission | Outgoing mail | 587 |
|
The possibility to use ports 25, 110, 143 and 587 either in the plain text (unencrypted) or secure (encrypted) mode comes from the Opportunistic TLS approach, according to which a STARTTLS command is invoked when an existing active plain text session is in place.
Technical side of using ports 465, 993 and 995 is similar to the way HTTP protocol is used over SSL/TLS: 1) secure ports are separated from their “unsecured” counterparts; 2) establishing an encrypted session precedes any data exchange.
NOTE: Although port 465 is not officially standardized in IANA’s documentation as the SMTPS port, it has been and is being used by mail server administrators for serving encrypted outgoing mail traffic.
In fact, both described techniques are commonly used in the Internet mail system nowadays, and a good security practice is to apply the SSL certificate on every mail port you are going to use.
Let’s move on and enable the SSL certificate for incoming and outgoing mail ports.
Port 25 (SMTP with STARTTLS)
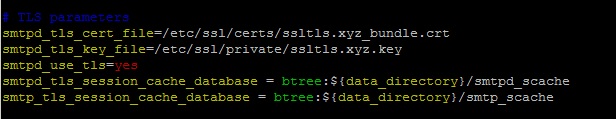
Open Postfix’s main.cf configuration file for editing. It is usually stored in the /etc/postfix/ directory. Find TLS parameters section inside main.cf and change the values of certain directives as shown below:
Close main.cf file with saving changes.
Ports 587 (Submission with STARTTLS) and 465 (SMTPS)
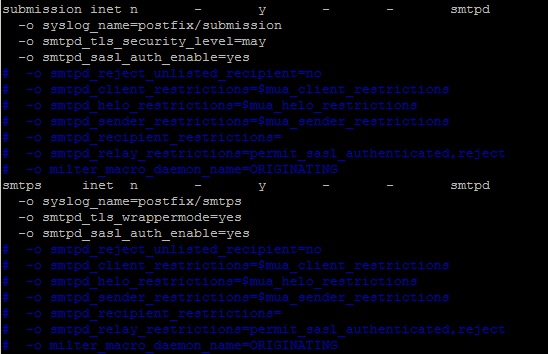
Open Postfix’s master.cf file located in the /etc/postfix/ directory and uncomment (and edit as below if needed) the following lines:
Now the master.cf file can be closed.
Ports 110 (POP3 with STARTTLS), 143 (IMAP with STARTTLS), 993 (IMAPS) and 995 (POP3S)
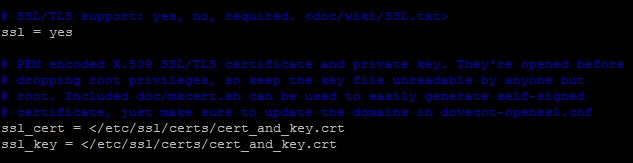
To enable the SSL certificate for Dovecot, open the 10-ssl.conf file, which is usually located in the /etc/dovecot/conf.d/ directory, and edit the following lines:
Now you can close the 10-ssl.conf file with saving changes. That’s it. After applying the above mentioned changes the certificate is installed for all incoming ports.
If your Dovecot version is 1.x, the SSL directives in configuration files are slightly different:
protocols = imap pop3 imaps pop3s
ssl_disable = no
- if the certificate and private key are saved in separate files
ssl_cert_file = </etc/ssl/certs/certificate.crt
sl_key_file = </etc/ssl/private/yourdomainname.key
- if the certificate and private key are saved in a single file
ssl_cert_file = </etc/ssl/certs/cert_and_key.crt
sl_key_file = </etc/ssl/certs/cert_and_key.crt
Advanced tweaks
This section contains a brief description of some additional settings that will come in handy for finetuning your mail server’s SSL/TLS handling. Feel free to read Postfix and Dovecot official documentation regarding this matter as well.
smtps inet n - n - - smtpd
-o smtpd_tls_wrappermode=yes
disable_plaintext_auth=yes
ssl_dh_parameters_length = 2048
ssl_cipher_list = ALL:!LOW:!SSLv2:!EXP:!aNULL
- for mandatory TLS
smtpd_tls_mandatory_exclude_ciphers = [cipher]
smtpd_tls_mandatory_protocols = ![protocol]
- for opportunistic TLS
smtpd_tls_exclude_ciphers = [cipher]
smtpd_tls_protocols = ![protocol]
- on Dovecot (/etc/dovecot/conf.d/10-ssl.conf)
ssl_prefer_server_ciphers = yes
- on Postfix (/etc/postfix/main.cf)
tls_preempt_cipherlist = yes
Checking SSL installation
Using OpenSSL
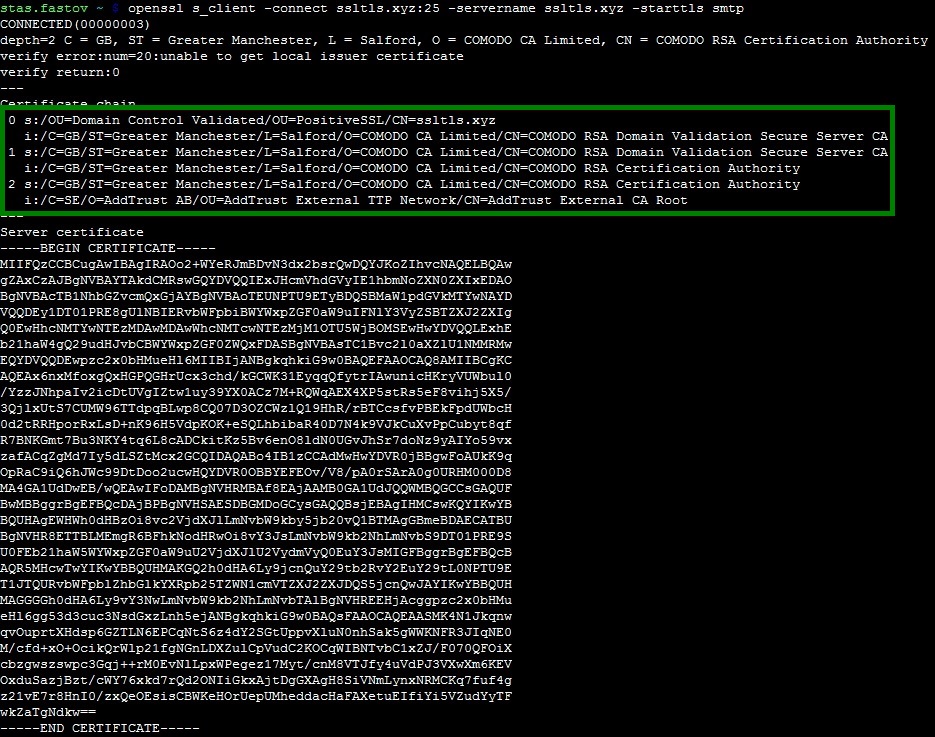
The OpenSSL toolkit allows checking SSL certificate installation on a server either remotely or locally. To check STARTTLS ports, run the following command replacing [port] with the port number and [protocol] with smtp, pop3 or imap value (see the example below) respectively:
openssl s_client -connect example.com:[port] -servername example.com -starttls [protocol]
The same command but without -starttls switch can be used for checking non-STARTTLS ports:
openssl s_client -connect example.com:[port] -servername example.com
Using online checkers
There is also a number of online tools which allow checking your mail server connectivity over SSL/TLS. You will need just to enter the server hostname and port number or an existing email account and run the test, which usually takes up to a few minutes. You can find the links to those testing tools below:
SSL-Tools
CheckTLS
MXToolbox
Need help? We're always here for you.