| Subtotal | $0.00 |
| Subtotal | $0.00 |
Installing SSL is easy with our installation service.
In order to activate your Certificate, you need a CSR code.
A CSR, or Certificate Signing Request, is a block of encoded text that you submit to a Certificate Authority when applying for an SSL Certificate.
It is typically generated on the server where the Certificate will be installed and should contain information about your website and business which will then be encoded into the Certificate.
Please ensure you fill out the CSR code details correctly. This should speed up the process of obtaining the SSL. Furthermore, the validation process for OV and EV SSL certificates requires that business details be entered accurately.
Generally, OpenSSL is used for CSR generation on Linux-based web servers (Apache or Nginx) So, if the default web server is installed, there should be no issues with using OpenSSL as it is installed by default on these web servers.
Now, you need to decide which key algorithm you want to use.
RSA key algorithm is the most commonly used algorithm nowadays. Click here for details.
ECDSA key algorithm is a modern technology that is used for the creation of ECC certificates. Details are here.
|
SSH Setup
The CSR will be generated on the server side, so you will need to connect to it via the SSH. SSH, also known as Secure Shell or Secure Socket Shell, is a Network protocol that gives users, particularly system administrators, a secure way to access a computer over an unsecured network. In order to connect to your server via SSH, you will need the IP-address, username, password and SSH client (any will do, for example: ZOC Terminal; PuTTY; OpenSSH; MobaXterm; SecureCRT) installed. The IP-address, username, and password can be obtained from your hosting provider. |
|
File location We recommend creating a folder to safely store the SSL files in. This folder can also be used to run the commands to generate the CSR. When you generate a CSR (.csr file), a Private key (.key file) will be generated at the same time. It is critical that you don’t lose the Private key as it will not be possible to get another one later. A Private key that corresponds to an SSL is necessary for installation. If you lose the Private key, you will need to generate another CSR and restart the whole process. Please do not share your Private key with anyone. This is bad practice; it must remain private at all times. One of the key reasons is that the Certificate Authority can revoke a certificate if its private key was compromised. You can create an SSL folder in your home directory as an alternative option. Please use the following command to do so:
Then, move to that folder by running:
|
The RSA algorithm is an asymmetric cryptography algorithm. This basically means that there are two keys involved while communicating, i.e., the Public key and Private key. The RSA key algorithm is the algorithm most widely used in digital security. You can refer to this article for more information.
You can run the following commands to generate the CSR. We recommend running this command in the folder where you will store the SSL files to avoid confusion later on.
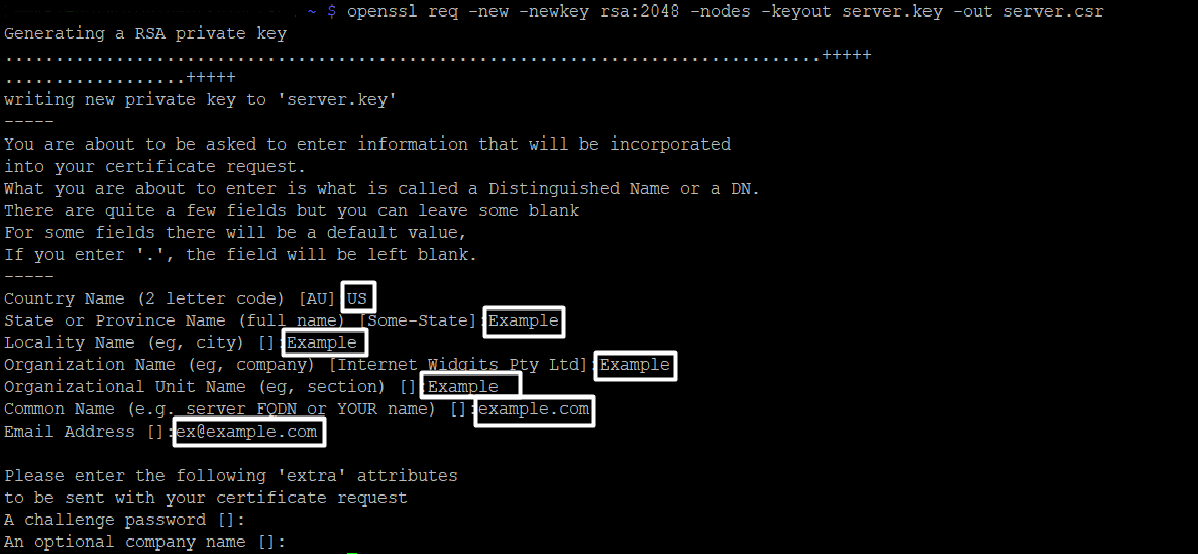
openssl req -new -newkey rsa:2048 -nodes -keyout server.key -out server.csr
Note! To avoid confusion, we recommend replacing server.key and server.csr with the real domain name the certificate will be issued for. Those will be underlined in the commands.
For example:openssl req -new -newkey rsa:2048 -nodes -keyout yourdomain_tld.key -out yourdomain_tld.csr "
When you run the command, you will be prompted to enter the values (Common name (CN), Locality (L), State (S), Country (C), Organization (O), Organization Unit (OU), Email Address) in the terminal. You can refer to this section to find out which information should be entered.
Warning! If the command fails, please refer to this section here.
The CSR should not contain characters such as '?', '@', '#', '$', '%', '^', '&' and '*' as they will cause issues. The only non-alphanumeric character permitted is the backslash '\'.
It is possible to generate a CSR with the following command:
openssl req -nodes -newkey rsa:2048 -keyout server.key -out server.csr -subj "/C=GB/ST=Yorks/L=York/O=My Company Ltd./OU=IT/CN=example.com"
You will need to specify the details in the command itself. You can refer to this section for the details that should be included.
|
Additional Flags in the CSR RSA
To generate a CSR code with the Street address value included, add the 'Subject' ('-subj') tool with the corresponding data to the command as follows:
The command with the zip code included in the address should look like this:
It is also possible to generate a CSR for a Multi-Domain SSL certificate via one line with all SANs (Subject Alternative Names).
|
The Elliptic Curve Discrete Logarithm Problem (ECDLP) needs to be solved in order to break the ECDSA key, and there has been no major progress so far to achieve this. Thus, an ECC certificate provides a better security solution and is more difficult to break using the usual hacker’s "brute force" methods.
You can run the following commands to generate a CSR. We recommend running this command in the folder where you will store the SSL files to avoid confusion in the future.
In the OpenSSL cryptographic library you can use this algorithm for CSR code generation by using the commands below:
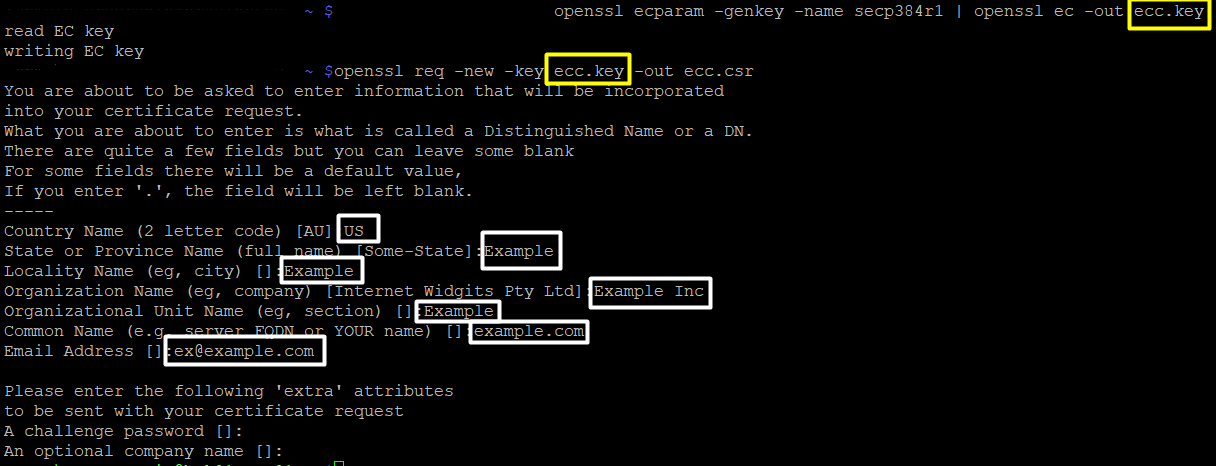
openssl ecparam -genkey -name secp384r1 | openssl ec -out ecc.key
openssl req -new -key ecc.key -out ecc.csr
Note! You will need to run the first command before running the second one as the CSR will be based on the key that’s generated by the first command. So, you need to make sure the name of the file matches.
Warning! If the command fails, please refer to the section here.
Example:
You run:openssl ecparam -genkey -name secp384r1 | openssl ec -out yourdomain.key
Then, the next command will be: openssl req -new -key yourdomain.key -out ec.csr
Note! When you run the second command, you will be prompted to enter the values (Common name (CN), Locality (L), State (S), Country (C), Organization (O), Organization Unit (OU), Email Address) right away in the terminal. For more information, refer to this section about which information should be entered.
Note! The CSR should not contain characters such as '?', '@', '#', '$', '%', '^', '&' and '*' as they will cause issues. The only non-alphanumeric character that can be used is the backslash '\'.
|
Additional Flags in the CSR ECC
It is also possible to generate a CSR for a Multi-Domain SSL certificate via one line with all SANs (Subject Alternative Names). The command can be modified with the -addext san extension as well as -subj to make a proper one liner:
|
Once you’ve generated your CSR you can use it to activate your SSL certificate.
To do this, you will need to copy the CSR code. Do this by running the command:
ls
You should see a list of the files present in the current folder.
Locate the file with the “.csr” extension and open it with this command:
cat filename.csr
Here, "filename" should be substituted with the name you specified in the CSR generation command.
The CSR code will begin and end with the following tags which should be copied too:
-----BEGIN CERTIFICATE REQUEST-----
-----END CERTIFICATE REQUEST-----
When you run the previously mentioned commands, you may encounter the following error message: “OpenSSL is not recognized as an internal or external command”
This could mean that the OpenSSL library was not installed or the %PATH% specified during the installation process was not correct.
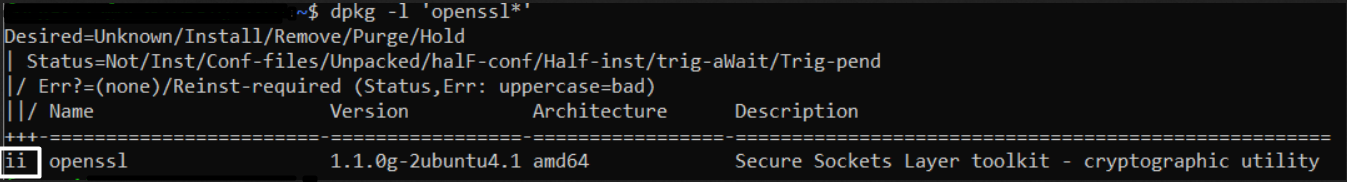
You can verify the installation of the OpenSSL library via this command:
dpkg -l 'openssl*'
You should get a response featuring “ii”. If the response does not contain “ii”, it means that there are issues with OpenSSL Libraries. If this is the case, you will need to contact your hosting provider/web-developer.
Need help? We're always here for you.